Why CVEs Are the Pulse of Your Network
In the modern enterprise, security is often viewed as a defensive wall. But a wall is only as strong as its bricks, and in the digital world, those bricks are constantly developing cracks. In the cybersecurity industry, we call these cracks CVEs (Common Vulnerabilities and Exposures).
While they might seem like just another string of alphanumeric jargon, CVEs are the universal language of risk. Understanding them is the difference between a proactive security posture and a frantic response to a data breach.
The Anatomy of a CVE: More Than Just a Number
A CVE is a unique identifier for a publicly disclosed cybersecurity vulnerability. Each entry—managed by the MITRE Corporation—provides a standardized way for security professionals to discuss and track specific flaws across different platforms.
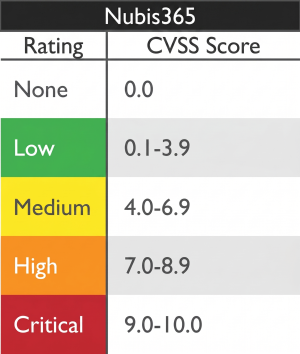
However, a CVE ID is just the name. The “weight” of the threat is determined by the CVSS (Common Vulnerability Scoring System). This is a numerical score from 0.0 to 10.0 that quantifies severity based on factors like:
- Attack Vector: Can it be exploited over the internet, or does the attacker need physical access?
- Complexity: Does it require “god-level” hacking skills, or can a script-kiddie trigger it?
- Privileges Required: Does the attacker need to be an admin, or can a guest user cause damage?
- Impact: Will it steal data (Confidentiality), delete files (Integrity), or crash the system (Availability)?
Why CVE Management is Your Most Important Daily Routine
The reality of 2026 is that adversaries are faster than ever. Once a CVE is published, the race begins. Hackers use AI to reverse-engineer patches and develop “Exploit PoCs” (Proof of Concepts) within hours.
If your organisation ignores CVEs, you are essentially leaving a map of your weaknesses on the front door. Managing CVEs is important because:
- It Prevents “Chain Attacks”: Attackers rarely use one flaw. They “chain” a low-severity CVE (like an information disclosure) with a high-severity one (like a sandbox escape) to fully take over a system.
- It Meets Compliance: Frameworks like GDPR, HIPAA, and PCI-DSS require that you maintain a “supported and patched” environment.
- It Protects Brand Reputation: Most major breaches in the last decade weren’t caused by sophisticated “Zero-Days,” but by old CVEs that had patches available for months but were never applied.
How to Deploy CVE Remediation: A 4-Step Playbook
Deploying a fix isn’t just about clicking “Update Now.” In a professional environment, you need a repeatable lifecycle.
Step 1: Discovery & Triage
You cannot fix what you don’t see. Use vulnerability scanners to map your environment. When a report comes in with 5,000 vulnerabilities, Triage is your best friend. Don’t look at the raw number; look at the Criticals (9.0+) first.
Step 2: Prioritization (The “So What?” Test)
A CVSS 10.0 on an isolated printer in the basement is less dangerous than a CVSS 7.5 on your primary Web Server. Layer in Business Context:
- Is the system internet-facing?
- Does it hold sensitive customer data?
- Is there an active exploit “in the wild”?
Step 3: Remediation Implementation
This is where the work happens. This could mean:
- Patching: The gold standard. Installing the vendor’s update.
- Configuration Changes: Disabling a vulnerable service (like the ANGLE engine in Edge).
- Compensating Controls: If you can’t patch a legacy system, put it behind a strict Firewall or VLAN.
Step 4: Verification
Never trust; always verify. After the patch is deployed, rescan the asset. If the scanner still sees the old binary—as we often see with “side-by-side” browser installs—your remediation failed.
Current Threat Landscape: April 2026 Key CVEs
To illustrate the diversity of threats, let’s look at some of the most critical vulnerabilities currently being tracked this month.
| CVE Identifier | Product Affected | CVSS Score | Description | Status |
| CVE-2026-6296 | Chromium (Chrome/Edge) | 9.6 (Critical) | Heap buffer overflow in ANGLE engine; allows Sandbox Escape. | Patch Available |
| CVE-2026-33824 | Windows IKE Service | 9.8 (Critical) | Remote Code Execution via secure key-management protocol. | Active Threat |
| CVE-2026-22769 | Dell RP4VMs | 10.0 (Critical) | Hardcoded admin credentials allowing full root access. | CISA KEV List |
| CVE-2026-32201 | SharePoint Server | 6.5 (Medium) | Active zero-day used for user spoofing and data modification. | Under Attack |
| CVE-2026-21533 | Windows Remote Desktop | 7.8 (High) | Elevation of Privilege; modifies service keys to add Admin users. | Patch Available |
Remediation Q&A
Q: What is a “Zero-Day”?
A: A Zero-Day is a vulnerability that is being exploited before the vendor is aware of it or has a patch ready. Once the vendor releases a fix, it becomes a “Standard CVE.”
Q: Why do some patches break my apps?
A: Vulnerability fixes often tighten security permissions or remove legacy code that old apps might rely on. This is why Testing in a sandbox environment is crucial before a global rollout.
Q: If my EDR blocks the attack, do I still need to patch the CVE?
A: Yes. EDR is your seatbelt, but patching is your brakes. You don’t want to rely solely on your seatbelt to survive every “accident.” Eventually, an attacker will find a way to bypass the EDR’s detection logic.
Q: Is it better to patch manually or use automated tools?
A: For a fleet larger than 10 PCs, Automation is mandatory. Manual patching is too slow to compete with the automated scanning tools used by modern threat actors.
